Emails: The Lifeline of Modern Communication
In today’s fast-paced digital world, emails have become an integral part of our daily lives. From personal to professional communication, emails have revolutionized the way we connect and interact with others. Let’s explore why emails are the lifeline of modern communication.
Efficiency and Speed
One of the key advantages of emails is their efficiency and speed. With just a few clicks, we can send messages across the globe in a matter of seconds. Gone are the days of waiting for traditional mail to arrive; emails provide instant communication that keeps us connected in real-time.
Versatility and Accessibility
Whether it’s a short message, a detailed report, or even multimedia attachments, emails offer unparalleled versatility. We can effortlessly send text, images, videos, and documents all within the same email thread. Moreover, with the advent of smartphones and tablets, accessing emails has become easier than ever before. We can stay connected on-the-go and respond promptly to important messages.
Formality and Professionalism
Emails have also transformed professional communication. They provide a formal platform for business correspondence that is essential in today’s corporate world. Emails allow us to maintain a professional tone while communicating with colleagues, clients, or business partners. They serve as a written record that can be referenced later if needed.
Organization and Archiving
Unlike physical letters or phone conversations, emails offer excellent organization capabilities. We can create folders to categorize different types of messages or prioritize them based on urgency. This makes it easier to locate specific information when needed. Additionally, email archives act as an invaluable resource for referencing past conversations or retrieving important attachments.
Global Connectivity
With emails being accessible worldwide, they bridge geographical gaps effortlessly. Whether you’re conducting business internationally or simply staying in touch with loved ones abroad, emails facilitate global connectivity like no other medium. Time zone differences are no longer obstacles; we can communicate at our convenience without worrying about disturbing others.
Privacy and Security
Emails also provide a level of privacy and security. Encryption protocols and spam filters help protect our messages from unauthorized access or unwanted solicitations. Additionally, we can control who has access to our emails by setting up passwords or using two-factor authentication.
In conclusion, emails have become an indispensable part of modern communication. Their efficiency, versatility, and accessibility make them an essential tool for personal and professional interactions. Emails have revolutionized the way we connect with others, enabling us to stay connected globally while maintaining privacy and security. As technology continues to evolve, emails will undoubtedly remain the lifeline of modern communication for years to come.
Frequently Asked Questions: Email Basics and Best Practices
- How do I create an email account?
- How do I check my emails?
- What is the best email service provider?
- How do I send an email attachment?
- How can I protect my emails from being hacked?
- What are the different types of emails?
- How do I set up an auto-reply message for my emails?
- What is the maximum file size limit for sending emails?
- How can I stop receiving unwanted emails (spam)?
How do I create an email account?
Creating an email account is a simple process that can be done in a few easy steps. Here’s a general guide on how to create an email account:
- Choose an Email Service Provider: There are several popular email service providers to choose from, such as Gmail, Outlook, Yahoo Mail, and many more. Visit their respective websites to proceed with the account creation process.
- Go to the Sign-Up Page: Once you have selected your preferred email service provider, navigate to their sign-up or create an account page. Look for a button or link that says “Sign Up” or “Create Account.”
- Provide Required Information: You will be prompted to enter some personal information, including your full name, desired email address, password, and sometimes additional details like phone number and alternative email address for account recovery purposes. Ensure the information you provide is accurate and secure.
- Choose an Email Address: Select a unique and memorable email address that reflects your identity or business (if it’s for professional use). Keep in mind that popular providers may have limited availability for common usernames.
- Set a Strong Password: Create a strong password that includes a combination of uppercase and lowercase letters, numbers, and special characters. This will help protect your account from unauthorized access.
- Complete Security Verification: Most email service providers will ask you to complete a security verification step to ensure you are not a robot or automated program trying to create an account.
- Agree to Terms of Service and Privacy Policy: Read through the terms of service and privacy policy of the email service provider before agreeing to them.
- Customize Account Settings (Optional): After creating your account, you may have the option to customize certain settings such as profile picture, signature, theme color, etc., based on the features offered by your chosen provider.
- Verify Your Account (If Required): Some email providers may require you to verify your account by clicking on a verification link sent to the email address you provided during the sign-up process. Follow the instructions in the email to complete the verification.
- Start Using Your Email Account: Once your account is created and verified, you can start sending and receiving emails using your new email address.
Remember to keep your login credentials safe and secure, and regularly update your password to ensure the security of your email account.
How do I check my emails?
To check your emails, follow these steps:
- Open your preferred web browser (e.g., Google Chrome, Mozilla Firefox, Safari).
- In the address bar, type in the website address of your email service provider. For example, if you use Gmail, enter “www.gmail.com” or if you use Outlook, enter “www.outlook.com”.
- Press Enter or Return on your keyboard to load the email service provider’s website.
- Once the website loads, you will typically see a login page where you need to enter your email address and password.
- Enter your email address in the designated field. Make sure to enter it correctly to avoid any login issues.
- Next, enter your password in the provided field. Ensure that you type it accurately as passwords are case-sensitive.
- If you want to save time logging in each time, you may have an option to check a box that says “Remember me” or “Keep me signed in.” Use this option only on trusted devices and not on public computers.
- After entering your login credentials, click on the “Sign In” or “Log In” button.
- The email service provider will verify your credentials and redirect you to your inbox or main email interface.
- Congratulations! You have successfully logged into your email account and can now view and manage your emails.
Once inside your inbox, you can read new messages, compose new emails, reply to or forward messages, organize emails into folders or labels (if available), and perform various other actions depending on the features provided by your email service provider.
Remember to log out of your email account when finished using it, especially if using a shared computer or a device that is not yours for security purposes.
What is the best email service provider?
Choosing the best email service provider depends on individual preferences and needs. There are several popular email service providers, each with its own set of features and benefits. Here are a few widely recognized options:
- Gmail: Developed by Google, Gmail is one of the most popular and widely used email services. It offers a clean user interface, ample storage space, powerful search capabilities, advanced spam filters, and integration with other Google services.
- Outlook.com: Formerly known as Hotmail, Outlook.com is Microsoft’s email service. It provides a user-friendly interface, intelligent inbox organization, integration with Microsoft Office tools, and Skype integration for video calls.
- Yahoo Mail: Yahoo Mail is another well-known email service that offers features such as a customizable interface, powerful search functionality, large attachment limit, and integration with Yahoo’s news and entertainment platforms.
- ProtonMail: ProtonMail stands out for its emphasis on security and privacy. It provides end-to-end encryption for emails and offers features like self-destructing messages and two-factor authentication.
- Zoho Mail: Zoho Mail is a popular choice for businesses as it provides professional email hosting services with custom domain options. It offers a clean interface, ample storage space, collaboration tools, and integration with other Zoho productivity apps.
Ultimately, the best email service provider will depend on your specific needs regarding storage space requirements, user interface preferences, security features desired (such as encryption), integration with other platforms or services you use regularly (like cloud storage or productivity tools), and any specific customization options you may require.
How do I send an email attachment?
Sending an email attachment is a straightforward process. Here’s a step-by-step guide on how to send an email attachment:
- Open your email client or webmail service: Launch the application or website where you access your email account.
- Compose a new email: Look for the “Compose” or “New Email” button to start creating a new message.
- Enter the recipient’s email address: In the “To” field, enter the email address of the person you want to send the attachment to. You can also add multiple recipients if needed.
- Add a subject: Write a concise and descriptive subject line that summarizes the content of your email.
- Compose your message: Write the body of your email, including any additional information or instructions you want to convey.
- Attach the file: Look for an icon or button that represents attaching files (usually depicted as a paperclip). Click on it, and a file explorer window will open.
- Locate and select the file(s): Navigate through your computer’s directories to find the file you want to attach. Click on it once to select it, or hold down Ctrl (or Command on Mac) while clicking to select multiple files simultaneously.
- Confirm attachment(s): After selecting your file(s), click on “Open” or “Attach” in the file explorer window, depending on your email client’s interface.
- Wait for uploading and attaching: The attached file(s) will be uploaded and attached to your email message. The time taken for this process may vary based on factors such as file size and internet speed.
- Review and send: Before sending, double-check that all necessary attachments are included by reviewing their names displayed in the email composition window. Once satisfied, click on “Send” to deliver your message along with its attachments.
- Confirmation: Depending on your email client, you may receive a notification confirming that your email, along with its attachments, has been sent successfully.
Remember to consider the file size and any potential restrictions on attachment sizes imposed by your email provider. If the file is too large to attach directly, you may need to compress it into a ZIP folder or use cloud storage services (like Google Drive or Dropbox) to share the file by including a link in your email.
That’s it! You have successfully sent an email attachment.
How can I protect my emails from being hacked?
Protecting your emails from being hacked is crucial to maintaining your privacy and security. Here are some important steps you can take to enhance the security of your email accounts:
- Strong Passwords: Use unique, complex passwords for each of your email accounts. Avoid common passwords and include a combination of uppercase and lowercase letters, numbers, and special characters. Regularly update your passwords and avoid reusing them across different platforms.
- Two-Factor Authentication (2FA): Enable 2FA for your email accounts whenever possible. This adds an extra layer of security by requiring a second verification step, such as a temporary code sent to your phone or a biometric scan.
- Be Wary of Phishing Attempts: Be cautious when clicking on links or downloading attachments in emails, especially if they are from unknown or suspicious sources. Phishing emails often try to trick you into revealing sensitive information or login credentials. Verify the legitimacy of the sender before taking any action.
- Keep Software Updated: Ensure that you regularly update your email client software (e.g., Outlook, Thunderbird) and operating system with the latest security patches and updates. Outdated software may have vulnerabilities that hackers can exploit.
- Secure Wi-Fi Networks: Avoid accessing your email accounts on public Wi-Fi networks, as they may be insecure and susceptible to eavesdropping attacks. If you need to use public Wi-Fi, consider using a virtual private network (VPN) for an added layer of encryption.
- Use Encrypted Connections: Ensure that you use secure protocols like SSL/TLS when accessing your email accounts through webmail or configuring email clients. This encrypts the data transmitted between your device and the email server.
- Regularly Backup Your Emails: Create backups of important emails regularly to protect against data loss due to hacking or accidental deletion. Consider using cloud storage services or local backups for added protection.
- Be Mindful of Account Recovery Options: Keep your account recovery options (such as alternate email addresses or phone numbers) up to date. This will help you regain access to your email account if it gets compromised.
- Use Antivirus and Anti-Malware Software: Install reputable antivirus and anti-malware software on your devices to detect and prevent any malicious software that could compromise your email security.
- Regularly Monitor Your Accounts: Keep an eye on your email accounts for any suspicious activity, such as unexpected password changes or unfamiliar emails in the Sent folder. If you notice anything unusual, report it to your email provider immediately.
By following these best practices, you can significantly reduce the risk of your emails being hacked and protect your sensitive information from falling into the wrong hands.
What are the different types of emails?
There are various types of emails that serve different purposes. Here are some common types:
- Personal Emails: These are informal emails exchanged between individuals for personal communication, such as staying in touch with friends and family, sharing updates, or sending invitations.
- Business Emails: Business emails are formal communications used for professional purposes within an organization or between businesses. They include emails related to inquiries, proposals, collaborations, project updates, and client communication.
- Marketing Emails: Marketing emails are sent by businesses to promote their products or services to potential customers. These can include newsletters, product announcements, discounts/offers, event invitations, or customer surveys.
- Transactional Emails: Transactional emails are automated messages triggered by specific user actions or events. These include order confirmations, shipping notifications, password resets, account updates, and receipts.
- Newsletters: Newsletters are regular email publications sent by organizations to subscribers who have opted in to receive updates. They often contain news articles, blog posts, industry insights, upcoming events, or exclusive content relevant to the subscribers’ interests.
- Welcome Emails: Welcome emails are sent to new subscribers or customers when they join a mailing list or make a purchase. They serve as a warm introduction and provide information about the company’s offerings or next steps.
- Event Invitation Emails: These emails invite recipients to attend conferences, webinars, workshops, product launches, or other events. They typically include event details like date, time, location (virtual/in-person), and registration information.
- Feedback/Survey Emails: Feedback or survey emails request customers’ opinions about products/services or their overall experience with a company. These help businesses gather valuable insights for improvement and customer satisfaction evaluation.
- Internal Communication Emails: Internal communication emails facilitate communication within an organization among employees and departments. They can include announcements from management, team updates/meetings reminders, policy changes/updates notifications.
- Follow-Up Emails: Follow-up emails are sent to remind recipients about a previous conversation, request, or meeting. They help maintain communication and ensure that important tasks or commitments are not overlooked.
Remember, the content and tone of each email type may vary depending on the context and audience. It’s important to tailor your emails accordingly to achieve effective communication and desired outcomes.
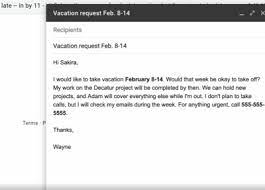
How do I set up an auto-reply message for my emails?
Setting up an auto-reply message for your emails is a convenient way to inform senders that you are currently unavailable and provide them with alternative contact information or an expected response time. Here’s a step-by-step guide on how to set up an auto-reply message:
- Open your email client or webmail interface: Depending on the email service you use, this could be Outlook, Gmail, Yahoo Mail, or any other email client.
- Locate the settings or options menu: Look for a gear icon or a menu button that indicates settings. Click on it to access the settings panel.
- Find the “Auto-reply” or “Vacation responder” option: In the settings panel, search for an option specifically related to auto-reply messages. It may be called “Auto-reply,” “Automatic replies,” “Out of Office,” or “Vacation responder.”
- Enable the auto-reply feature: Once you’ve found the appropriate option, toggle it on to activate the auto-reply functionality.
- Configure your auto-reply message: You will typically find fields to enter your subject line and message content. Craft a concise and informative message that includes details such as your unavailability dates, reason for absence, and alternative contact information if necessary.
- Set the duration of the auto-reply: Specify the start and end dates for your auto-reply if applicable. Some email clients also allow you to set different messages for internal contacts (colleagues) and external contacts (clients).
- Customize additional settings (if available): Depending on your email client, you may have additional options such as setting specific times when the auto-reply should be active each day or choosing whether to send replies to all incoming messages or only once per sender.
- Preview and save your changes: Before saving, review your auto-reply message for accuracy and clarity. Once satisfied, save your changes to activate the auto-reply feature.
- Test your auto-reply: To ensure everything is working correctly, send a test email to your own email address or ask a colleague to send you one. Check if the auto-reply message is delivered as expected.
- Disable the auto-reply when you return: Once you’re back and no longer need the auto-reply message, remember to go back to your email settings and turn off the auto-reply feature.
Remember, the steps may vary slightly depending on your specific email client or webmail interface. If you encounter any difficulties, consult the help documentation or support resources provided by your email service provider for more detailed instructions.
What is the maximum file size limit for sending emails?
The maximum file size limit for sending emails can vary depending on the email service provider and the specific settings they have in place. However, as a general guideline, most email providers have a file size limit ranging from 10 to 25 megabytes (MB) for attachments. It’s important to note that some providers may have lower limits or may impose additional restrictions on certain file types for security reasons.
To send larger files, there are alternative methods you can consider:
- File compression: Compressing files into a ZIP or RAR format can reduce their size and make them more manageable for email attachments.
- Cloud storage services: Upload the files to a cloud storage service like Google Drive, Dropbox, or Microsoft OneDrive and share the download link with the recipient via email.
- File transfer services: Use dedicated file transfer services like WeTransfer or SendSpace, which allow you to upload large files and generate download links that can be shared via email.
It’s always a good idea to check with your specific email service provider or consult their documentation for accurate information regarding their file size limits and any additional guidelines they may have in place.
How can I stop receiving unwanted emails (spam)?
Dealing with unwanted emails, commonly known as spam, can be frustrating. However, there are several effective strategies you can implement to minimize and stop receiving spam:
- Use a Spam Filter: Most email providers offer built-in spam filters that automatically detect and divert spam emails to a separate folder. Make sure your spam filter is enabled and periodically check the spam folder to ensure legitimate emails haven’t been mistakenly marked as spam.
- Be Cautious with Your Email Address: Avoid sharing your email address indiscriminately, especially on public platforms or untrustworthy websites. Spammers often scrape the internet for email addresses, so consider using alternate or disposable email addresses for online registrations or subscriptions.
- Unsubscribe from Legitimate Mailing Lists: If you receive unwanted emails from legitimate sources, look for the unsubscribe link usually located at the bottom of the email. Clicking on it will remove you from their mailing list. Exercise caution when unsubscribing from unknown or suspicious senders, as it may confirm that your email address is active.
- Don’t Respond or Click on Suspicious Emails: Interacting with suspicious emails can alert spammers that your email address is active and encourage them to send more spam. Avoid clicking on unfamiliar links or downloading attachments from unknown senders.
- Use Disposable Email Addresses: Consider using temporary or disposable email addresses when signing up for newsletters, promotions, or online services that require an email address but may lead to potential spamming.
- Keep Your Software Updated: Ensure that your operating system, web browser, and antivirus software are up to date with the latest security patches and updates. This helps protect against potential vulnerabilities exploited by spammers.
- Be Wary of Phishing Attempts: Spammers often use phishing techniques to trick users into revealing personal information or login credentials through deceptive emails. Be cautious of emails asking for sensitive information and verify the legitimacy of any requests before responding.
- Report Spam: Most email providers have options to report spam or mark emails as junk. By reporting spam, you help improve the filtering systems and protect others from similar unwanted emails.
Remember, while these strategies can significantly reduce the amount of spam you receive, it may not eliminate it entirely. Stay vigilant and regularly review your email settings to ensure optimal spam protection.